What is a watering hole attack?
A watering hole attack is a security exploit in which the hacker intends to compromise a targeted group of end users by infecting websites that they’re sure many people visit. The objective is to infect this group of users computer and get access of their respective workplaces. Targeted organizations can include the defense sector, government, heath care, banking, education etc. The attacker looks for weaknesses and vulnerabilities in the organization’s cyber security system.
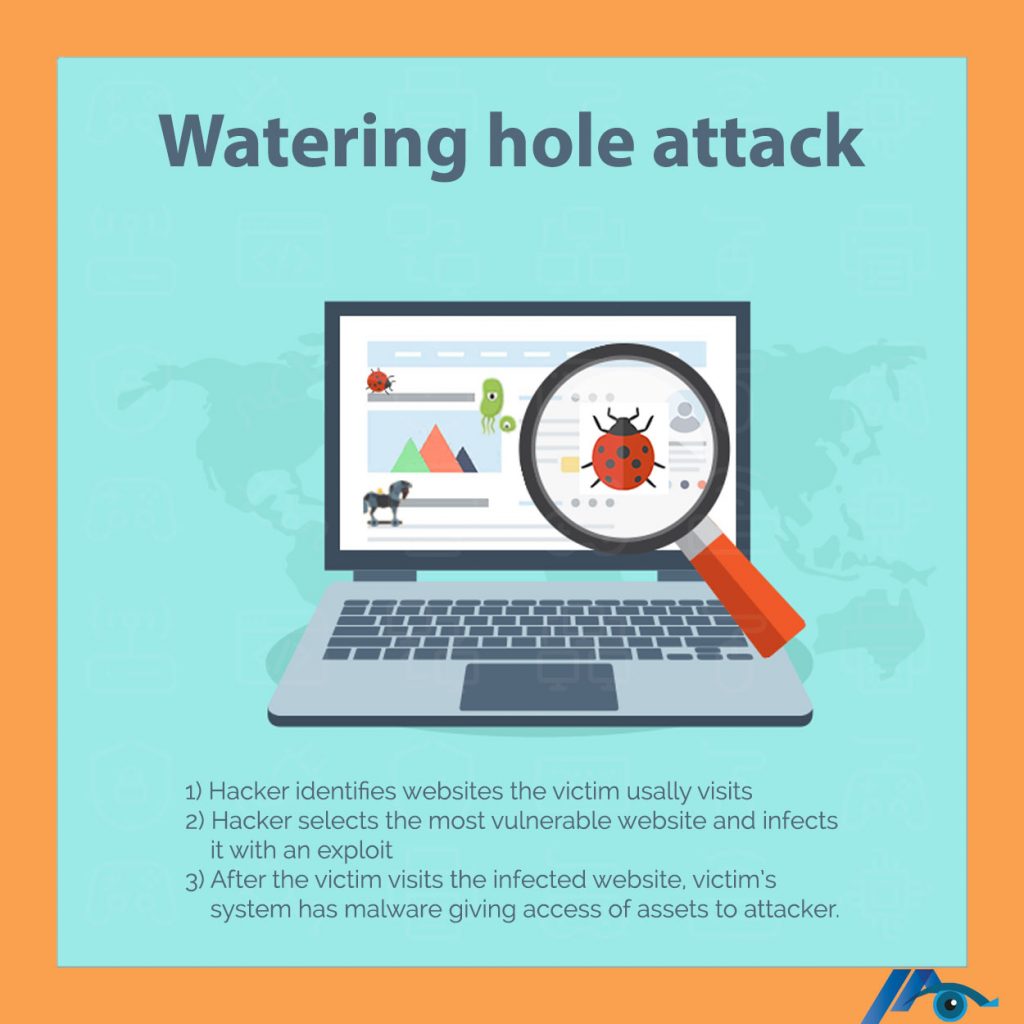
How do watering hole attacks work?
This involves a series of events started by a hacker to get a foothold inside the organizations system. First, the attacker chooses a website or a service the potential victim is using and knows well. Usually, this target site will have low security. The hacker compromises the website and injects a code payload into the website. When the victim visits the compromised site the payload is triggered and it starts to exploit a chain of exploits to infect the victims computer. The payload can start working automatically or a fake prompt appears instructing the user to download the malicious code.
Once the payload has been triggered on, the hacker now has access to the assets on the network and uses that computer to pivot attacks for further damage. Other damages can include gathering information about victim. The attacker can also use the victims computer to exploit other networks.
How to prevent a watering hole attack
These steps and operational requirements can help to avoid watering hole attacks:
Organizations can protect themselves against watering hole attacks with advanced targeted attack protection solutions as well as some simple steps e.g. dynamic malware solutions, web gateways etc.
- Use the best and latest practices for cyber security. Since watering hole attacks are frequent web exploits, following published best practices and strict guidelines can avoid the exploit chain from running.
- Never allow personal use of corporate resources. Block access to websites not used for work, and do not allow users to access websites for personal communication.
- Do not add trusts to third-party sites. Some sites require additional permissions to run properly. Audit or simply don’t allow these exceptions, as they may allow an attacker to use the site in the future.
- Provide training for users to recognize unlikely behavior and evade violations. Users may be careless with sites they commonly visit, so they should be trained to not click on suspicious links or bypass security warnings.
- Scan and monitor internet traffic. Use web proxies that can scan content in real time; monitor for common exploits; and use web logging to detect suspicious activity.
Examples of watering hole attacks
Watering hole attacks have been around for some time. Here are some notable examples of past attacks:
- In 2012, several sites were compromised, including the U.S. Council on Foreign Relations (CFR). The attack used the Gh0st Rat exploit and was known as the VOHO attacks.
- In 2016, the Canada-based International Civil Aviation Organization (ICAO) spread malware that infected the United Nations (UN) network.
- In 2017, Ukrainian government websites were compromised to spread the ExPetr malware.
- In 2019, many religious and humanitarian websites were compromised to target specific Asian communities.
Miracle technologies solutions for Watering Hole attacks
Miracle Technologies Inc. platform is built upon years of unmatched experience at AT&T Labs Research and renowned Wall Street MSPs. Rated #1 IT Support Company NYC, Managed IT Services Provider, IT Consulting Firm, Cyber Security Provider since 2008.
- Our NY based fortified managed IT services security shield includes:
- Enterprise firewalls (Checkpoint, Cisco, PaloAlto, Sonicwall, Fortinet, Watchguard…)
- IPS (Intrusion Prevention), IDS (Intrusion Detection)
- Anti-Virus, Anti-Spyware, Anti-Malware, Anti-Ransomware
- Email gateways and proxy servers
- Cyber security including email cyber security
- MFA (Multifactor Authentication) solutions
Free IT Quote: (646)237-4472
myteam@miracletechs.com